SAVANNAH GUTHRIE'S MOM MISSING: DAY 37
YouTube · p9O2UDR2oYo
Quick Read
Summary
Takeaways
- ❖A vandalized utility box near Nancy Guthrie's home was initially suspected of causing an internet outage to facilitate a kidnapping, but experts suggest it was likely unrelated to Wi-Fi and possibly an act of copper theft or simple vandalism.
- ❖Digital forensic experts emphasize that Google and Apple continuously collect extensive location data (every 30 seconds, 3-10 meter radius) from devices, even in the background, which can be retrieved with a search warrant to reconstruct a person's movements and activities.
- ❖Modern vehicles' infotainment and telematics systems also record significant data, including routes, phone calls, text messages, and even driving habits (braking, ignition turns), which can be extracted forensically.
- ❖The FBI's Tattoo and Graffiti (TAG) team at Quantico utilizes vast databases and AI-driven tools to analyze and identify individuals based on even small portions of tattoos, linking them to organized crime or other groups.
- ❖Forensic analysis of blood drops on Nancy Guthrie's porch suggests a low-velocity aspiration (cough or sneeze) from close range, raising concerns about the failure to collect a doormat that could contain additional evidence.
- ❖Popular theories circulating online, such as Nancy Guthrie having a heart attack, family involvement in her disappearance, or a Chilean robbing crew being responsible, are largely dismissed by experts due to lack of empirical evidence and inconsistencies with known facts.
Bottom Line
Google and Apple collect passive location data at high frequency (every 30 seconds, 3-10 meter accuracy) from user devices, even without active navigation, retaining this data for the life of the account unless manually deleted.
This pervasive data collection offers investigators a powerful, detailed timeline of a suspect's movements, parking locations, and daily routines, far beyond traditional cell tower dumps.
Individuals should be aware of the extent of their digital footprint and privacy implications. For law enforcement, this data stream represents a consistently available, high-resolution investigative tool.
Modern car infotainment and telematics systems independently record extensive data, including GPS routes, phone calls, text messages, music played, and even driving events like braking and ignition cycles.
This transforms vehicles into mobile forensic goldmines, providing a secondary or primary source of location and activity data that is separate from personal mobile devices.
Vehicle manufacturers are sitting on vast, untapped data reservoirs that could be standardized for forensic access, potentially aiding in countless investigations. For consumers, understanding their car's data collection policies is increasingly important.
The FBI's Tattoo and Graffiti (TAG) team at Quantico employs AI-driven tools and massive image databases to reconstruct and identify tattoos from partial or obscured images, linking them to known individuals or groups.
This specialized forensic capability allows investigators to leverage seemingly minor visual evidence (like a sliver of a tattoo on a blurry video) to generate significant leads, even when traditional identification methods fail.
Advancements in AI and image recognition will continue to enhance forensic capabilities, making it harder for individuals to conceal identity through physical markings. For security and intelligence agencies, investing in such specialized teams and technologies is a high-yield strategy.
Lessons
- Understand that your digital footprint is extensive: Google, Apple, and even your car collect vast amounts of data on your location and activities, which can be accessed by law enforcement with proper warrants.
- Be critical of online theories in ongoing investigations: Many popular theories lack empirical proof and can distract from factual analysis, as seen with the utility box, heart attack, and Chilean gang theories.
- Recognize the importance of meticulous evidence collection in crime scenes: The failure to collect a doormat with potential blood evidence highlights how critical every item can be for forensic analysis.
Quotes
"Most folks don't realize just how much data they create every day. Just through a normal course of business, every day of their lives, they're creating data points that they they couldn't even comprehend."
"If you were going to the extent to attack a utility infrastructure, you would probably know that that was not going to affect how the internet service is delivered."
"These are not from a great height and it's highly concentrated, Nancy. I I think that uh my theory here is that this is blood that originates from the nasoperinex area."
Q&A
Recent Questions
Related Episodes
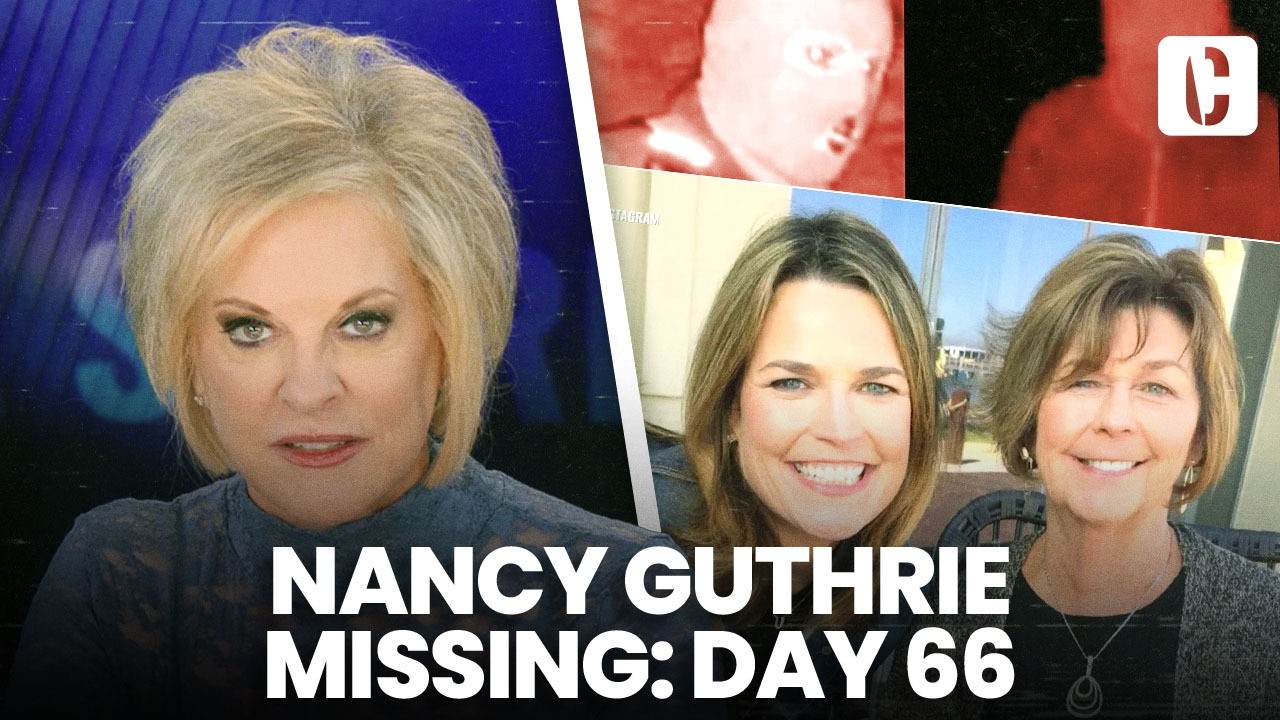
SAVANNAH GUTHRIE'S MOM MISSING: DAY 66
"On day 66 of Nancy Guthrie's disappearance, investigators grapple with two distinct sets of Bitcoin ransom notes, digital tracing challenges, and potential physical evidence like shoe coverings, as new, dubious claims emerge from a 'hyena' seeking payment for information."

Student Murders Her Ex-Teacher After Graduation
"A welfare check for a missing retired teacher escalates into a murder investigation when his car is found with a former student, revealing a brutal robbery-homicide driven by drug-induced rage."

Hell On Wheels: Mackenzie Shirilla's Double Murder Crash
"A seemingly accidental car crash that killed two young men in Strongsville, Ohio, was meticulously uncovered by investigators to be a deliberate act of double murder by the 17-year-old driver, Mackenzie Shirilla, amidst a tumultuous relationship and a shocking lack of remorse."

The Root Beer Float Murder | Full Episode + Post Mortem
"A seemingly natural death of a husband is unmasked as a calculated poisoning plot by his wife and stepdaughter, revealed only after an unrelated burglary exposes a trail of incriminating text messages."